prads: Passive Real-time Asset Detection System
Is a `Passive Real-time Asset Detection System`. It passively listens to network traffic and gathers information on hosts and services it sees on the network. This information can be used to map your network, letting you know what services and hosts are alive/used, or can be used together with your favourite IDS/IPS setup for “event to host/service” correlation.
Features
PRADS is under development, but it currently includes:
* OS fingerprinting, both SYN and SYN+ACK (IP/TCP) (Compatible with p0f fingerprints)
* TCP service fingerprinting (Signatures from/compatible with pads)
* TCP discovery of hosts (SYN and SYN+ACK)
* UDP discovery of hosts
* UDP OS fingerprinting
* ARP discovery of hosts
* MAC vendor fingerprinting (from ARP data)
* ICMP discovery of host
* ICMP OS fingerprinting
* perl DBI support (sqlite (default), MySQL, PostgreSQL, Oracle, MSSQL…)
* Daemon mode
* Some packet statistics (received,dropped,drop-rate and dropped by interface)
Installation
#### PRADS INSTALL
# apt-get install prads
### or, from source
## dependencies
libpcap0.8 (>= 0.9.8), libpcre3 (>= 8.10), libresolv
# On an Ubuntu system:
$ sudo apt-get install rst2man libpcap0.8-dev libpcre3-dev
$ git clone git://github.com/gamelinux/prads.git
$ cd prads
$ make
$ sudo make install
# On a FreeBSD system (C version)
$ pkg_add -r pcre git gmake py26-docutils
$ git clone git://github.com/gamelinux/prads.git
$ cd prads
$ gmake
*Note: Installer doesn't work on FreeBSD, so manually copy, or symlink, the binary and config files.
### Compile-time options
remember to `make clean` first!
## Static install
$ make static
## Build with debug options
$ make debug
## Profiling prads
$ make profile
## use perftools faster malloc
$ make TCMALLOC=y
## Profile with perftools
$ make TCMALLOC=y PPROF=y debug
## the newest, fastest libpcap into prads
$ git clone git://bpf.tcpdump.org/libpcap
$ cd libpcap && ./configure --disable-dbus && make -j2 && cd ..
$ make PCAPDIR=libpcap
*Note* that prads will now always look for libpcap in that directory!
Use
Quickstart:
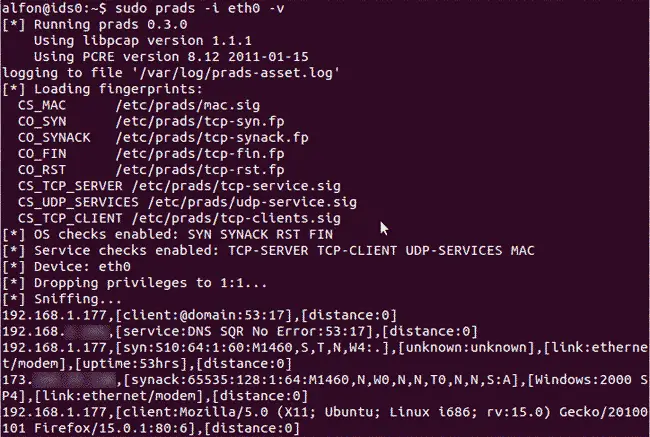
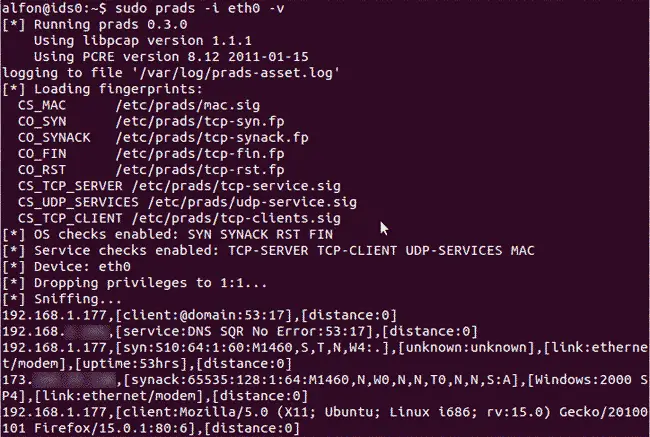
root@machine# prads -D [*] Running prads 0.2.0 [*] Using libpcap version 1.1.1 [*] Using PCRE version 7.8 2008-09-05 [*] OS checks enabled: SYN SYNACK RST FIN ACK [*] Service checks enabled: TCP-SERVER TCP-CLIENT UDP-SERVICES ARP [*] Device: eth0 [*] Daemonizing...
To see the raw asset log file:
root@machine# tail -f /var/log/prads-asset.log asset,vlan,port,proto,service,[service-info],distance,discovered 84.24.154.213,0,1268,6,ACK,[65392:118:1:0:.:A:Windows:XP],10,1277044697 109.87.38.106,0,56393,6,ACK,[16425:114:1:0:.:A:Windows:XP],14,1277044697 192.168.2.43,0,38359,6,SYN,[S4:64:1:60:M1460,S,T,N,W7:.:Linux:2.6 (newer, 7):link:ethernet/modem:uptime:2630hrs],0,1277044698 192.168.2.43,0,48065,6,ACK,[54:64:1:0:N,N,T:ZAT:Linux:2.6:uptime:2630hrs],0,1277044697 76.99.73.67,0,55834,6,ACK,[33069:48:1:0:N,N,T:AT:Linux:2.4(newer)/2.6:uptime:307hrs],16,1277044697 65.191.159.39,0,48747,6,ACK,[259:114:1:0:N,N,T:AT:unknown:unknown:uptime:20hrs],14,1277044697
Remember that ACK mode is and always will be rather unreliable.
To get a better view of the detected systems, run the following command:
prads-asset-report | less 13 ------------------------------------------------------ IP: 109.87.38.106 OS: Windows Server 2008 (R2 Standard 64-bit) (60%) 1 [..crop..] 104 ----------------------------------------------------- IP: 192.168.2.43 OS: Linux 2.6 (newer, 7) (100%) 3 MAC(s): 00:DE:AD:BE:EF:2F (2010/06/20 16:39:00)
Source: https://github.com/gamelinux/